Communication between hosts can happen only if they can identify each other on the network. In a single collision domain (where every packet sent on the segment by one host is heard by every other host) hosts can communicate directly via MAC address. MAC address is a factory coded 48-bits hardware address which can also uniquely identify a host. But if a host wants to communicate with a remote host, i.e. not in the same segment or logically not connected, then some means of addressing is required to identify the remote host uniquely. A logical address is given to all hosts connected to Internet and this logical address is called Internet Protocol Address.
An IP host address identifies a device to which IP packets can be sent. An IP network address identifies a specific network segment to which one or more hosts can be connected. The following are characteristics of IP addresses:
• IP addresses are 32 bits long
• IP addresses are divided into four sections of one byte (octet) each
• IP addresses are typically written in a format known as dotted decimal
Note: Binary Numbers:
IP addresses are 32 bits long. The 32 bits are divided into four octets (8-bits). A basic understanding of binary numbering is very helpful if you are going to manage IP addresses in a network because changes in the values of the 32 bits indicate either a different IP network address or IP host address.
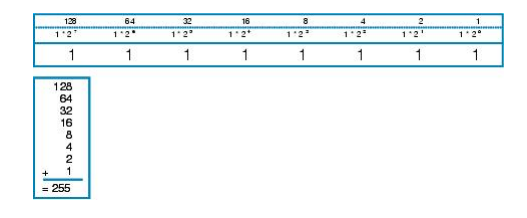
A value in binary is represented by the number (0 or 1) in each position multiplied by the number 2 to the power of the position of the number in sequence, starting with 0 and increasing to 7, working right to left. The figure below is an example of an 8-digit binary number.
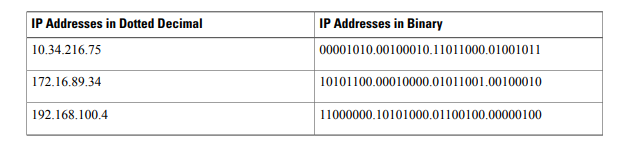
The table below shows some examples of IP addresses.
IPv4 Addressing Classes
Internet Protocol (IP) is of 32 bit i.e 4 bye in decimal form. IP address has 5 classes i.e Class A, Class B, Class C, Class D and Class E.
Class A : 0-127 (127 is reserved for loopback)
Class B : 128-191
Class C : 192-223
Class D : 224-239 (Reserved for Multicasting)
Class E : 240-255 (Reserved for R&D and DOD)
IP addresses is also divided into Public(Used over Internet) and Private IP( Can used by Private Company) addresses. Class A 10.0.0.0 to 10.255.255.255, Class B172.16.0.0 to 172.31.255.255 and in Class C 192.168.0.0 to 192.168.255.255 is Private address and rest are Public Address.
IPv4 Addressing Demo
- enable
- configure terminal
- interface type number
- no shutdown
- ip address ip-address mask
- end
Router>enable
Router# configure terminal
Router(config)# interface fastethernet 0/0
Router(config-if)# ip address 192.168.0.1 255.255.255.0
Router(config-if)# no shutdown
Router(config-if)# end
Troubleshooting Tips
The following commands can help troubleshoot IP addressing:
• show ip interface –Displays the IP parameters for the interface.
• show ip route connected –Displays the IP networks the networking device is connected to
IP Subnetting
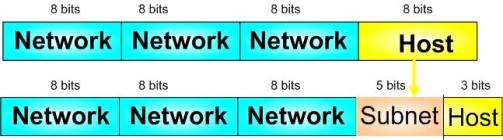
Subnet or Subnetwork is a logically dividing of an IP Address. The process of dividing a network into two or more networks is called subnetting. Creating subnetworks is essentially the act of taking bits from the host portion of the address and reserving them to define the subnet address instead. Clearly this will result in fewer bits being available for defining your hosts.
For the subnet address scheme to work, every machine on the network must know which part of the host address will be used as the subnet address. This condition is met by assigning a subnet mask to each machine. A subnet mask is a 32-bit value that allows the device that’s receiving IP packets to distinguish the network ID portion of the IP address from the host ID portion of the IP address. This 32-bit subnet mask is composed of 1s and 0s, where the 1s represent the positions that refer to the network subnet addresses.
Classless Inter-Domain Routing (CIDR)
CIDR allows the creation of networks of a size other than those allowed with the classful subnetting by allowing more than the three classful subnet masks. It’s basically the method that Internet service providers (ISPs) use to allocate a number of addresses to a company, a home—their customers. They provide addresses in a certain block size.
For example, a Class A default subnet mask, which is 255.0.0.0. This tells us that the first byte of the subnet mask is all ones (1s), or 11111111. When referring to a slash notation, you need to count all the 1-bits to figure out your mask. The 255.0.0.0 is considered a /8 because it has 8 bits that are 1s—that is, 8 bits that are turned on. A Class B default mask would be 255.255.0.0, which is a /16 because 16 bits are ones (1s): 11111111.11111111.00000000.00000000.
Example:
255.0.0.0 – /8
255.128.0.0 – /9
255.255.0.0 – /16
255.255.240.0 – /20
Subnetting easy steps
Step 1. Get Block size
Subtract the last octate of subnetmask from 256
i.e 256 -[last octate sm]= ?
Step 2. Get number of Subnets
i.e no, of subnets = (2)n
here n=how many bits in last octate are used
Step 3. Know the Valid host number
i.e number of valid host = (2)H-2
here h= unused bits on last octate and 2 is subtracted for broadcast and network id
Subnetting example – Class C
Q: Subnet 192.168.10.1/25
Here, IP = 192.168.10.1 & Subnet mask = 255.255.255.128
Step 1. Block Size
256-128=128
Step 2. No. of Subnets
(2)n=21=2
Step 3. No. of valid host
(2)H-2=27-2=126
When we subnet 192.168.10.1/25 we get 2 subneted network with block size 128 where 126 host are valid.
i.e
Subnet 1.
192.168.10.0—-192.168.10.127
Subnet 2.
192.168.10.128—–192.168.10.256
Note: In class C subnetting changes occurs in 4th octates. In class B subnetting changes occurs in 3rd octate and in class A subnetting changes occurs on 2nd octate.
Subnetting is of two types VLSM (Variable length subnet mask) and FLSM (Fix length subnet mask). The above done is FLSM. which means the length of subnetwork is fixed as processed. In VLSM ;you can manually divide single network into multiple subnetwork as per requirement. IN FLSM block size is fixed and in VLSM block size can be adjusted according to requirement.
Let’s see the example of VLSM.
Q: 192.168.10.0/25
Requirement 110 IPs, then subnet by /26
total IP available are 128
Requirement 30 IPs then subnet by /30
total ip available are 32
Requirement 14 then subnet by /6
total IP available are 16
By this you can save Ip addresses also as in FLSM you can not subnet as per requirement and there can be wastage of IPs.