A Network Packet Broker (NPB) resides between taps and SPAN
Microsoft Sentinel is a scalable, cloud-native, security information and event
Shadow IT is the use of information technology systems, devices,
Blurring your background makes your surroundings appear out of focus
Endpoint device security is most important concern for every for
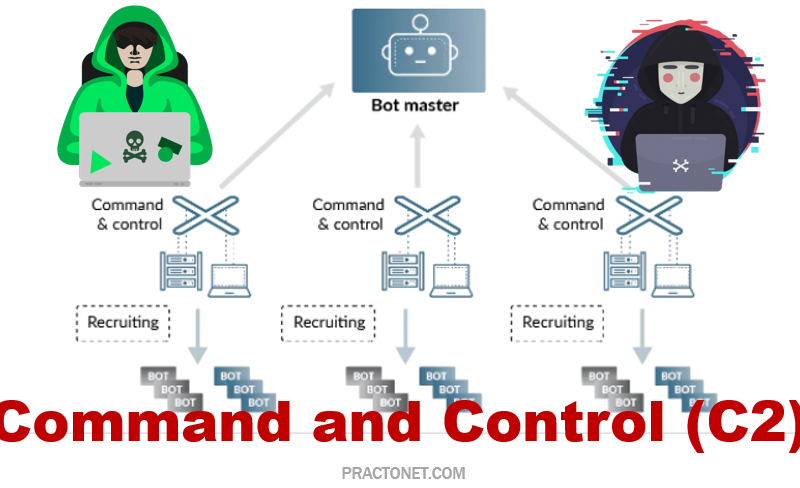
Malicious network attacks have been on the rise in the
The OWASP Top 10 is a standard awareness document for
Windows Server Update Services (WSUS) and System Center Configuration Manager
SD-WAN is a virtual WAN architecture that provides multi-branch organizations
When it comes to computers, the difference between 32-bit and