A session is the period of time when you as
Request for Comment 1918 (RFC 1918), “Address Allocation for Private
Penetration testing is also known as pen testing or ethical
Upgrading software is continuous and non ending process for networking
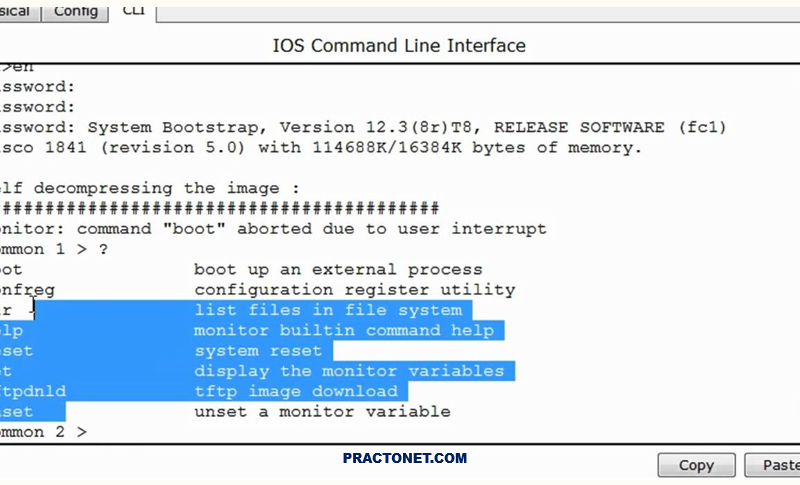
In order to reset a router’s password you must use
Burp Suite is a collection of different tools which are
It is often observed that term information system and information
Cyber Incident Response Planning is always on the radar of
Endpoint security is the practice of securing endpoints or entry
The Cyber Kill Chain offers a comprehensive framework as a