A DMZ or demilitarized zone is a perimeter network that
Request for Comment 1918 (RFC 1918), “Address Allocation for Private
Upgrading software is continuous and non ending process for networking
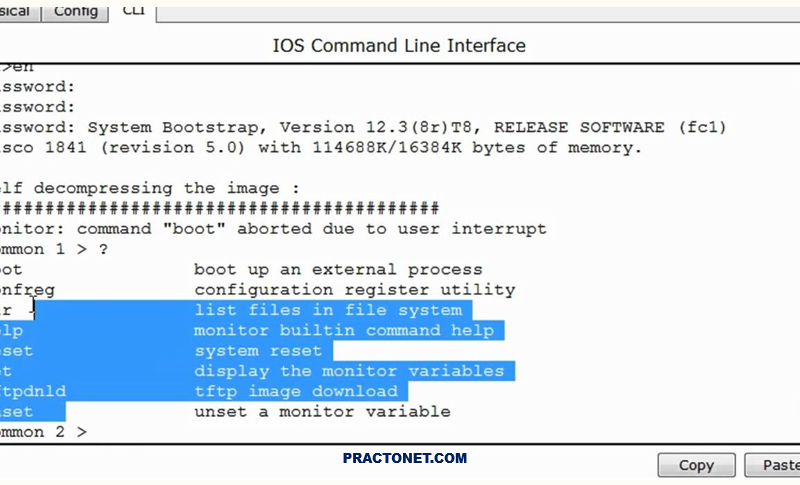
In order to reset a router’s password you must use
Endpoint security is the practice of securing endpoints or entry
A Network Packet Broker (NPB) resides between taps and SPAN
Windows Server Update Services (WSUS) and System Center Configuration Manager
SD-WAN is a virtual WAN architecture that provides multi-branch organizations
Blockchain is a shared, immutable ledger that facilitates the process
A “Firewall” is one of the most popular computer and